Anthony Timbers: Blog

Why Your Business Should Be Aware of the Microsoft Exchange Server Remote Code Execution Vulnerability
At the start of March and over the past few weeks, there has been an active exploitation of vulnerabilities observed in the Microsoft Exchange on-premises products. At this time, these exploits are not known to affect Microsoft 365 or Azure. If there is a successful exploitation seen from these vulnerabilities it will allow an attacker to access on premises Exchange servers, which in turn will enable them to gain persistent system access and control of an enterprise network. The current vulnerabilities related to this exploitation activity include CVE – 2021 – 26855, CVE – 2021 – 26857, CVE – 2021 – 26858, and CVE – 2021 – 27065. According to the Microsoft security researchers, these CVE’s are related but are not known to have been exploited: CVE – 2021 – 26412, CVE – 2021 – 26854, and CVE – 2021 – 27078.
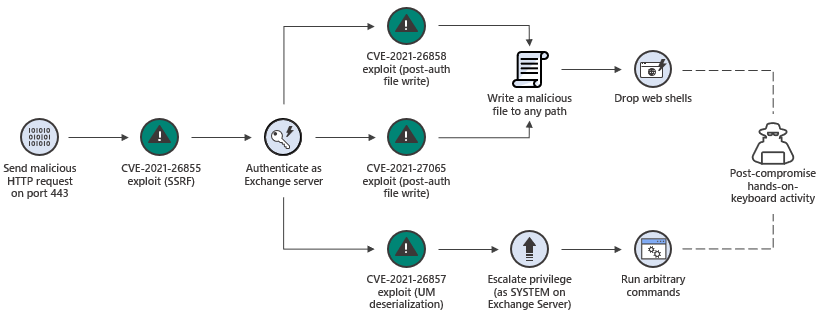
The way that the attack is started is explained from the CVE write ups. These write ups show that this vulnerability is part of an attack chain and the initial attack requires the ability to make an untrusted connection to Exchange server port 443. This can be protected against by restricting untrusted connections and/or setting up a VPN to separate the Exchange server from external access. To learn more about this attack you can look at the following video link. https://youtu.be/w-L3gi4Cexo
Using this mitigation will only protect against the initial portion of the attack. Other portions of the chain can be triggered if an attacker already has access or can convince an administrator to open a malicious file. Currently, this exploit affects Microsoft Exchange servers 2013, 2016, and 2019. It’s expected that these attacks will most likely increase in the upcoming months, as attackers start to investigate and automate the exploitation of these vulnerabilities. Not all the footholds have been put in place at this time and it is expected they will be put in place for future exploitations. At this if you are still running Exchange 2003 and 2007 it is not supported but is believed to not be affected by these vulnerabilities. Exchange 2010 is only affected by CVE-2021-26857 which is not the first step in this attack. These vulnerabilities are being actively exploited by multiple adversary groups. For the highest assurance, block access to vulnerable Exchange servers from untrusted networks until your Exchange servers are patched or mitigated.
Some response steps that can be taken to help protect yourself from these exploits is to make sure that you are able to communicate with your team without an attacker eavesdropping on any of your communications. Using isolated accounts or other means of communication that is not in house is recommended. The next thing you can do is deploy the oncoming exchange updates to the affected exchange servers with are Microsoft exchange 2013, 2016, and 2019 to help better protect them. It is recommended that you prioritize updating and mitigation of the vulnerability. For new updates on how to handle this vulnerability for you can go to /https://msrc-blog.microsoft.com/2021/03/16/guidance-for-responders-investigating-and-remediating-on-premises-exchange-server-vulnerabilities/ this will be updated as more information about this come out.
If for whatever reason find that you are unable to update your exchange servers, there are still a few mitigation tactics that can be used to handle these vulnerabilities. One mitigation method you can do is by doing hunts on the exchange server themselves. Some of the things that can be hunted are the IOCs, known web shells, and analyze the exchange logs. Other things you can do is investigate your environment for exploitation and indicators of persistence and remediate any of the exploitations that are identified. Investigate your environment for indicators of lateral movement or further compromise. Some other ways to mitigate the threat are listed below.
- Implement an IIS Re-Write Rule to filter malicious https requests.
- Disable Unified Messaging (UM)
- Disable Exchange Control Panel (ECP) VDir
- Disable Offline Address Book (OAB) VDir
If you do find any evidence of exploitation, ensure you are retaining those logs and use the details such as timestamps and source IPs to drive further investigation. Remediate and quarantine them for further investigation unless they are expected customizations in your environment.
If any of your security detections or the investigation tools results lead you to suspect that your Exchange servers have been compromised and an attacker that has actively engaged in your environment. It is highly recommended to execute your Security Incident Response plans, and possibly engage with an experienced Incident Response assistance. It is particularly critical if you suspect that your Exchange environment is compromised by a persistent adversary. You must coordinate your response using alternative communications channels as mentioned earlier in this document.
Not sure if you are affected by this vulnerability? Anthony Timbers LLC can investigate and run vulnerability scans for you to determine if you are vulnerable. Schedule a consultation by following the link below and we can explain how we can help you detect this vulnerabiilty and even help you protect your assets from compromise in case it is exploited:
