Anthony Timbers: Blog

What Is The Difference Between Penetration Testing And Vulnerability Scanning?
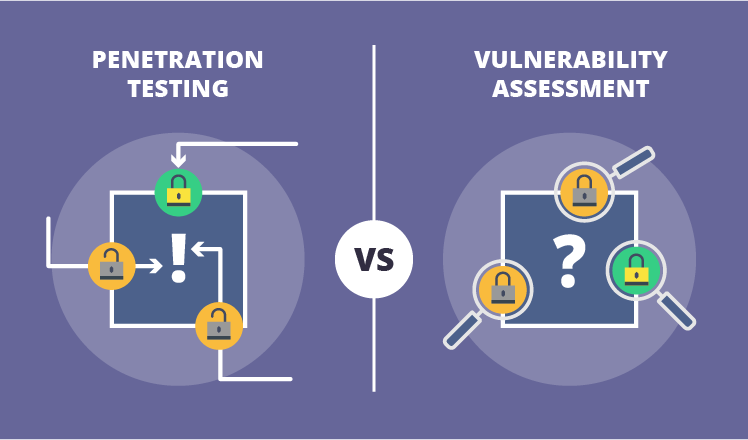
Penetration testing and vulnerability assessments are often used interchangeably and confused as being one and the same thing. If this is you, don’t worry, you’re not the only one and this blog is going to break it down for you and hopefully you can remember the difference without the help of google. To be clear, both are very necessary and are vital in ensuring your business is as secure as it can be since it’s impossible to make everything completely secure. Throughout my career I’ve seen a scary number of businesses approach security through obscurity, penetration testing and vulnerability assessments are tools used to easily expose this dire weakness. In simple words penetration testing = exploiting vulnerabilities while vulnerability assessments = discovering vulnerabilities. Both, however, have a similar end goal of reducing the attack surface by understanding what parts of the organization need more attention in order to be more properly secured.
What is a Vulnerability Assessment?
A vulnerability assessment, also referred to as a vulnerability scan, is more automated in nature and can be completed more frequently. Typically an organization conducts vulnerability scans on at least a quarterly basis, but we recommend that you conduct vulnerability scans more frequently on a weekly basis or monthly, to identify weaknesses in the organization’s security posture. The output of a vulnerability assessment is a report that lists out the different vulnerabilities identified during the scan with a risk designation typically of “low”, “moderate” or “high”. Those marked as high obviously have a higher priority in remediation. A popular tool used in vulnerability scanning is Tenable Nessus, a tool that is used primarily here at Anthony Timbers LLC to conduct scans for our clients. We highly recommend Nessus due to its ease of use and its efficiency. Scans are normally run by administrators or security personnel with a good understanding of cybersecurity and vulnerabilities. This is important because vulnerability scanning typically has the limitation of producing false positives, meaning the scanning tool identifies a threat that is not real. With that, it’s important to have an individual that can properly evaluate the results.
What is Penetration Testing?
Penetration Testing, also often referred to as ethical hacking, is a much more in-depth service than a vulnerability assessment, in that the person performing this type of service is looking for any way by any means to get into a business’s system/network. This type of work requires a highly skilled professional and should be manual in nature. Depending on the size of the organization, a penetration test can take up to a couple of weeks to complete. An Ethical hacker will often discover and exploit vulnerabilities that are not known to normal business processes. The ethical hacker is knowledgeable in different exploitation methods but is also free, depending on the rules of engagement, to even attempt a physical breach of the organization’s facility. There are five stages to penetration testing:
Reconnaissance involves gathering information about the target network in preparation for an attack. This typically includes gathering information that is publicly available on the Internet (trust me, there is a TON available if you use the right tools). Scanning involves conducting various scans like port scans and vulnerability scans to find a weakness to exploit. Gaining access involves launching attacks in order to gain access to the target’s network. Maintaining access typically involves installing backdoors so that the attacker can always come back to the network and also attempting to escalate privileges and find sensitive data. Covering tracks simply involves removing traces that an attack ever happened by modifying logs and other data. These steps together will give you a good idea of how secure your network is and where your holes are.
In Closing
Often, businesses confuse which service is needed and ask for one when they really need the other. I hope this article was helpful in:
- Understanding the difference between Penetration Testing and Vulnerability Assessments, and;
- Giving you a better understanding of which service is right for your current business needs
Do I Need A Penetration Test Or A Vulnerability Assessment??
If you are still unsure on which service you think you need for your business, schedule some time with us to discuss the right choice for you based on your business needs here: Schedule A Consultation
As a closing point, a good analogy to use to remember the difference between a vulnerability assessment and penetration testing is: A vulnerability assessment is like walking up to your door, checking to see if it’s unlocked and stopping there. A penetration test will not only check to see if the door is unlocked, but it also attempts to open the door and walk right in.